Rise by Six: Your Daily Dose of Inspiration
Explore insights and stories that elevate your day.
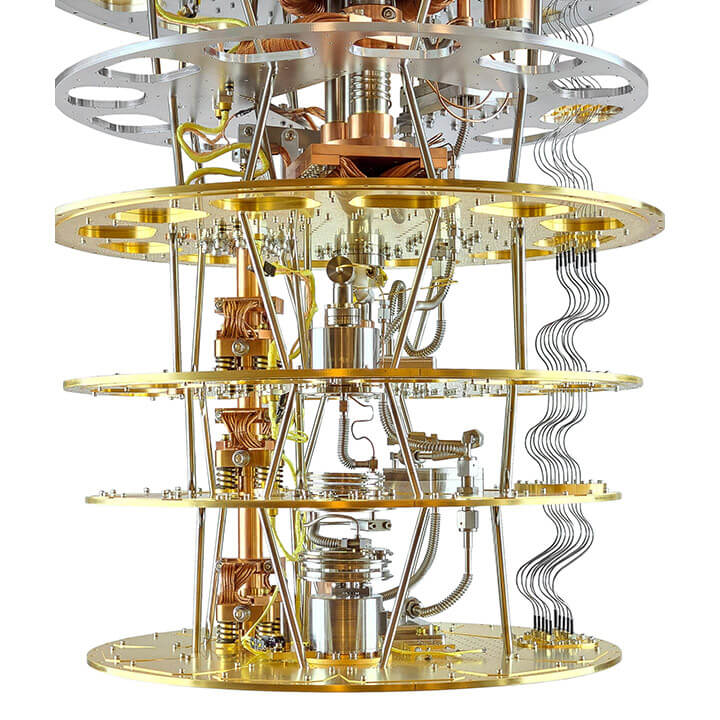
Quantum Computing: Are We Ready for the Codebreakers' Revolution?
Unleash the future! Discover how quantum computing could transform security and unleash a new era of codebreakers. Are we prepared?
Understanding Quantum Computing: The Basics Explained
Quantum computing represents a revolutionary approach to computation that harnesses the principles of quantum mechanics to process information in fundamentally different ways compared to classical computers. At its core, quantum computing utilizes quantum bits, or qubits, which can exist in multiple states simultaneously due to the phenomenon known as superposition. This capability allows quantum computers to perform complex calculations at speeds unattainable by conventional systems. Moreover, techniques like quantum entanglement enable qubits to become interconnected such that the state of one qubit instantly influences the state of another, regardless of distance, enriching the computational abilities available for solving intricate problems.
To better grasp the potential of quantum computing, it's essential to understand its key components: superposition, entanglement, and quantum interference. Superposition enables qubits to represent both 0 and 1 simultaneously, drastically increasing the computational power. Entanglement creates a unique correlation between qubits, which can be leveraged to perform coordinated operations that classical systems find challenging to execute efficiently. Lastly, quantum interference allows quantum algorithms to enhance the probability of correct answers while diminishing the chances of incorrect ones. As research continues to evolve, the potential applications of quantum computing span various fields, from cryptography to drug discovery, promising to alter the technological landscape profoundly.
The Potential Impact of Quantum Computers on Cybersecurity
The advent of quantum computers holds the potential to revolutionize many areas of technology, and cybersecurity is at the forefront of this transformation. Unlike traditional computers that rely on bits, quantum computers utilize qubits to perform complex calculations at unprecedented speeds. This capability poses both opportunities and challenges; for instance, quantum algorithms could enhance encryption methods, making them more robust against threats. However, the same technology could also render current encryption protocols obsolete, putting sensitive data at greater risk than ever before.
As the race for quantum supremacy progresses, cybersecurity experts are working hard to anticipate and mitigate the risks associated with this emerging technology. Organizations must begin to adopt quantum-resistant encryption methods to protect their data. Potential strategies include using lattice-based or hash-based cryptography, which are believed to be more secure against quantum attacks. It is crucial for companies and individuals to stay informed about the developments in quantum computing to safeguard their sensitive information effectively in a world where quantum computers could overturn traditional security measures.
Are Today's Cryptographic Systems Vulnerable to Quantum Attacks?
As quantum computing technology advances, the question arises: are today's cryptographic systems vulnerable to quantum attacks? Traditional cryptographic algorithms, such as RSA and ECC, rely on the difficulty of certain mathematical problems. However, quantum computers leverage principles of quantum mechanics to solve these problems exponentially faster. For instance, Shor's algorithm can factor large numbers in polynomial time, posing a potential threat to the widely-used RSA encryption. As a result, the cryptographic community is actively researching and developing quantum-resistant algorithms to ensure data security in a post-quantum world.
Despite the looming threat, it's essential to understand that practical quantum computers capable of breaking current cryptographic systems are still in their infancy. Organizations worldwide are moving towards implementing quantum-safe solutions, but the transition requires careful planning and execution. Simultaneously, experts recommend enhancing existing systems with hybrid approaches that combine traditional and post-quantum cryptography. By doing so, we can bolster defenses against potential quantum attacks while continuing to utilize current technologies until new standards are widely adopted.